DoH Erodes Privacy
 Mozilla, through firefox, is as of the end of September, going to be rolling out the forcing of DoH, or DNS over HTTPS for users of firefox, with the U.S.A first on the rollout. Google and others are also following, but in a very much limited way, where as firefox, will be blanket enabled.
Mozilla, through firefox, is as of the end of September, going to be rolling out the forcing of DoH, or DNS over HTTPS for users of firefox, with the U.S.A first on the rollout. Google and others are also following, but in a very much limited way, where as firefox, will be blanket enabled.So why is DoH so bad you ask?
DoH is currently at least, only paired with Cloudfares DNS services, this is fraught with danger, as Cloudfare does log requests and keeps them for about one month based on their original announcement, and even if they now claim they wont be logging when its fully operational, it's still very dangerous, because it's also centralising the Internet, sending all your DNS queries to one company, as you can imagine, doing so is incredibly dangerous and wrong!
As one who is a stickler for privacy (pretty evident if you've read a few of my posts), DoH must be pretty f'ked up for me to come out against it, Mozilla claims this is all about privacy, but that's something 90% of us already have.
DoH for most of us will be a huge step backwards actually eroding our privacy, since most ISP's, especially here in Australia (even with the data retention laws) and Europe with the GDPR do not log DNS requests, and giving all your DNS requests to Cloudfare is as good as giving them to the likes of the NSA, it'll be like all their Christmases came at once.
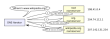 You also need to understand this alleged privacy offered by DoH is because of how DNS works only between your computer and the Cloudfare servers anyway, the Cloudfare servers then follow the usual lookup paths using the normal clear transmission methods, all of which are unencrypted, from the root servers to the server providing them with the address relating to your lookup. So any privacy from DoH is severely limited to the first hop in a line of many.
You also need to understand this alleged privacy offered by DoH is because of how DNS works only between your computer and the Cloudfare servers anyway, the Cloudfare servers then follow the usual lookup paths using the normal clear transmission methods, all of which are unencrypted, from the root servers to the server providing them with the address relating to your lookup. So any privacy from DoH is severely limited to the first hop in a line of many.
DoH may be of use to some living under totalitarian governments, but, if you're that worried, you'd probably be using Tor anyway.
Other problems with DoH is that some ISP's and Network Operators use, and some force the use of, local DNS resolvers for the purpose of protecting users from vile sites like the worst of the worst such as kiddie porn, well known malware and phishing fraud sites, then there's the DNS operators who provide family style G-rated clean feeds who block gambling and pretty much all porn sites, a method used by many religious based institutions and educational facilities, government mandated site blocking for piracy as used in Australia and others (DNS based blocking is the most friendly and acceptable method by ISP's and users alike, even with the courts knowing how easy it is to bypass, its that sweet spot everyone looked for).
 Mozilla at least, is now starting to listen to Network, Security, and Cleanfeed Operators, they have acknowledged networks have legitimate uses for keeping control of their DNS, they accept that many people run their own home local bind caching servers and want to keep control locally - at least in the immediate and foreseeable future anyway, so Mozilla have enabled what they term a "canary" domain, that is, a domain that will be looked up in local DNS by firefox, and if that domain does not get a response, firefox will automatically disable DoH for the remainder of that session, resulting in your local DNS resolvers being used,
Mozilla at least, is now starting to listen to Network, Security, and Cleanfeed Operators, they have acknowledged networks have legitimate uses for keeping control of their DNS, they accept that many people run their own home local bind caching servers and want to keep control locally - at least in the immediate and foreseeable future anyway, so Mozilla have enabled what they term a "canary" domain, that is, a domain that will be looked up in local DNS by firefox, and if that domain does not get a response, firefox will automatically disable DoH for the remainder of that session, resulting in your local DNS resolvers being used,
This test is conducted at the start of a session, ie: when you first open firefox, if it gets a response to its canary domain however, DoH stays enabled for that session. It does not according to Mozilla, do periodic checks.
Users can permanently disable DoH themselves by navigating in firefox to
Settings->Network Settings then unticking the Enable DNS of Https checkbox, or by using about:config and setting network.trr.mode to a value of 5
Network Operators can also influence this for the time being by forcing NXDOMAIN type responses, an example with bind is:
... that's it, no other content, now you know why its called empty
Test your results...
A normal lookup which will not disable DoH would result in a response such as
A protected lookup, thus disabling DoH would result n
It is also feasible to assume that in the future there will be other services paired with Mozilla for DoH, it's possible Mozilla may withdraw the canary domain test, which will result in Network Operators taking far more drastic measures like outright blocking DoH servers, there is a distributed list of DoH servers that also contains some small operators who are trying out for their networks, which kind of defeats the purpose since they should be the only ones seeing it anyway - they are, their users first hop
Other Browsers
Google's Chrome will as of v78 (scheduled for release next month) also enable DoH, however only if you are using Cleanbrowsing, Cloudflare, DNS.SB, Google, OpenDNS, and Quad9 as your DNS services, if you are using your local resolvers, in release 78, at least, it will not force DoH onto you - again, this is acceptable in my view. This is also subject to change in the future. If users of the above DNS services do not want to use DoH, they can disable DoH support by modifying the chrome://flags/#dns-over-https flag.
At the time of this writing there is some debate over if this will work on those using linux, it is likely Google will exclude linux users in the early stages, but again, this if true, would also be subject to change in the future.
Opera also has the ability to use DoH in the developer release 65.0.3430.0, but it is disabled by default - a very sensible decision. There at present is no word from Microsoft, but you can bet they too will be watching this very closely as well.
DoH may be of use to some living under totalitarian governments, but, if you're that worried, you'd probably be using Tor anyway.
Other problems with DoH is that some ISP's and Network Operators use, and some force the use of, local DNS resolvers for the purpose of protecting users from vile sites like the worst of the worst such as kiddie porn, well known malware and phishing fraud sites, then there's the DNS operators who provide family style G-rated clean feeds who block gambling and pretty much all porn sites, a method used by many religious based institutions and educational facilities, government mandated site blocking for piracy as used in Australia and others (DNS based blocking is the most friendly and acceptable method by ISP's and users alike, even with the courts knowing how easy it is to bypass, its that sweet spot everyone looked for).
 Mozilla at least, is now starting to listen to Network, Security, and Cleanfeed Operators, they have acknowledged networks have legitimate uses for keeping control of their DNS, they accept that many people run their own home local bind caching servers and want to keep control locally - at least in the immediate and foreseeable future anyway, so Mozilla have enabled what they term a "canary" domain, that is, a domain that will be looked up in local DNS by firefox, and if that domain does not get a response, firefox will automatically disable DoH for the remainder of that session, resulting in your local DNS resolvers being used,
Mozilla at least, is now starting to listen to Network, Security, and Cleanfeed Operators, they have acknowledged networks have legitimate uses for keeping control of their DNS, they accept that many people run their own home local bind caching servers and want to keep control locally - at least in the immediate and foreseeable future anyway, so Mozilla have enabled what they term a "canary" domain, that is, a domain that will be looked up in local DNS by firefox, and if that domain does not get a response, firefox will automatically disable DoH for the remainder of that session, resulting in your local DNS resolvers being used, This test is conducted at the start of a session, ie: when you first open firefox, if it gets a response to its canary domain however, DoH stays enabled for that session. It does not according to Mozilla, do periodic checks.
Users can permanently disable DoH themselves by navigating in firefox to
Settings->Network Settings then unticking the Enable DNS of Https checkbox, or by using about:config and setting network.trr.mode to a value of 5
Network Operators can also influence this for the time being by forcing NXDOMAIN type responses, an example with bind is:
zone "use-application-dns.net" {
type master;
notify no;
file "empty";
};
The empty file contents typically used for badsite blocking are well suited here, which contains $TTL 3600
@ IN SOA localhost. abuse.localhost. (
999
10800
10800
259200
3600
)
NS localhost.
... that's it, no other content, now you know why its called empty
Test your results...
A normal lookup which will not disable DoH would result in a response such as
~$ host -t A use-application-dns.net
use-application-dns.net has address 63.245.208.212
A protected lookup, thus disabling DoH would result n
~$ host -t A use-application-dns.net
use-application-dns.net has no A record
It is also feasible to assume that in the future there will be other services paired with Mozilla for DoH, it's possible Mozilla may withdraw the canary domain test, which will result in Network Operators taking far more drastic measures like outright blocking DoH servers, there is a distributed list of DoH servers that also contains some small operators who are trying out for their networks, which kind of defeats the purpose since they should be the only ones seeing it anyway - they are, their users first hop
Other Browsers
Google's Chrome will as of v78 (scheduled for release next month) also enable DoH, however only if you are using Cleanbrowsing, Cloudflare, DNS.SB, Google, OpenDNS, and Quad9 as your DNS services, if you are using your local resolvers, in release 78, at least, it will not force DoH onto you - again, this is acceptable in my view. This is also subject to change in the future. If users of the above DNS services do not want to use DoH, they can disable DoH support by modifying the chrome://flags/#dns-over-https flag.
At the time of this writing there is some debate over if this will work on those using linux, it is likely Google will exclude linux users in the early stages, but again, this if true, would also be subject to change in the future.
Opera also has the ability to use DoH in the developer release 65.0.3430.0, but it is disabled by default - a very sensible decision. There at present is no word from Microsoft, but you can bet they too will be watching this very closely as well.
Comments
Display comments as Linear | Threaded